Manifest: Wednesday 10 October 2001
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ @ WARNING: HOST IDENTIFICATION HAS CHANGED! @ @@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ IT IS POSSIBLE THAT SOMEONE IS DOING SOMETHING NASTY! Someone could be eavesdropping on you right now (man-in-the-middle attack)! It is also possible that the host key has just been changed. Please contact your system administrator. Add correct host key in /af10/evans/.ssh/known_hosts to get rid of this message. Agent forwarding is disabled to avoid attacks by corrupted servers. X11 forwarding is disabled to avoid attacks by corrupted servers. Are you sure you want to continue connecting (yes/no)? yes
| Assignments Due | |
| Now | Problem Set 3 | Wednesday, 17 October | No Class | Wednesday, 24 October | Midterm | Monday, 29 October | Full Proposal Due |
- MBC, Chapter 21. (It is not necessary to understand all the details of the different random number generators, but you should understand how they work in general.)
- Brad Arkin, Frank Hill, Scott Marks, Matt Schmid, Thomas John Walls, and Gary McGraw. How we Learned to Cheat in Online Poker: A Study in Software Security. Gary McGraw will give a guest lecture in CS588 on Monday, 29 October.
- (optional) Neil Haller. The S/KEY One-Time Password System. Symposium on Network and Distributed System Security, 1994.
- (optional) Ronald Rivest, Adi Shamir. PayWord and MicroMint: Two simple micropayment schemes, 1996. Two clever digital cash systems for small transactions.
- (optional) Alma Whitten, J.D. Tygar. Why Johnny Can't Encrypt: A Usability Evaluation of PGP 5.0, 1999.
- eCash Technologies, CyberCash (now owned by VeriSign)
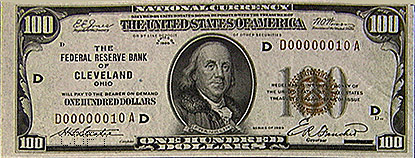
- US Government Accounting Office report on Counterfeit U.S. Currency Abroad
- Security features of new (1996) US currency. Note that the form to report a counterfeit note is an unsigned Windows executable!
Blind Signatures
- Alice picks random k between 1 and n.
- Send's Bank t = mke mod n. (e from the Bank's public key.)
- Bank signs t using private key d. Sends Alice:
td = (mke mod n)d mod n = (mke)d mod n ≡ mdked mod n
= (mke)d mod n ≡ mdked mod n≡ mdk mod n. - Alice divides by k to get sm = md mod n.
Digital Cash Protocol
(Based on Bruce Schneier, Applied Cryptography: Protocols, Algorithms, and Source Code in C, 2nd Edition. Section 6.4 has an excellent presentation of digital cash protocols.)-
Alice prepares n money orders each containing:
- Amount
- Uniqueness String: X
- Identity Strings: I1 = (h(I1L), h(I1R)), ..., In = (h(InL), h(InR)).
Each (IiL, IiR) pair reveals Alice's identity, I = IiL XOR IiR.
h is a secure, one-way hash function.
- Alice blinds (multiplies by random k) all n money orders and sends them to bank.
- Bank asks for any n - 1 of the random kis and all its corresponding identity strings.
- Bank checks money orders. If okay, signs the remaining blinded money order, and deducts amount from Alice's account.
- Alice unblinds the signed note, and spends it with a Merchant.
- Merchant asks Alice to randomly reveal either IiL or IiR for each i. (Merchant chooses random n-bit selector string.)
- Alice sends Merchant corresponding IiLs or IiRs.
- Merchant uses h to confirm Alice didn't cheat.
- Merchant takes money order and identity string halves to bank.
- Bank verifies its signature, and checks uniqueness string. If it has not been previously deposited, bank credits Merchant and records uniqueness string and identity string halves.
- If it has been previously deposited, bank looks up previous identity string halves. Finds one where both L and R halves are known, and calculates I to identify Alice. Arrests Alice.
- If there are no i's, where different halves are known, arrest Merchant.
- What is cash? What is it good for?
- What properties should digital cash have?
- How can someone sign something without knowing what it is?
- How is this useful to be able to sign something without knowing what it is? How is it dangerous?
- How does the digital cash protocol work?