Digital Cash Protocols
Properties of Physical Cash
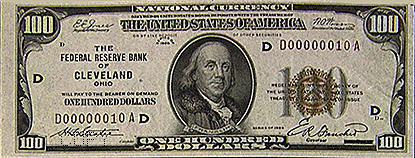
- Universally recognized as valuable
- Easy to transfer
- Anonymous
- Heavy
- Moderately difficult to counterfeit in small quantities
- Extremely difficult to get away with counterfeiting large quantities
Digital Cash, Protocol Attempt #1
- Alice prepares 100 money orders for $1000 each.
- Puts each one in a different sealed envelope, with a piece of carbon paper.
- Gives envelopes to bank.
- Bank opens 99 envelopes and checks they contain money order for $1000.
- Bank signs the remaining envelope without opening it (signature goes through carbon paper).
- Bank returns envelope to Alice and deducts $1000 from her account.
- Alice opens envelope, and spends the money order.
- Merchant checks the Banks signature.
- Merchant deposits money order.
- Bank verifies its signature and credits Merchants account.
Digital Cash, Protocol Attempt #2
- Alice prepares 100 money orders for $1000 each, adds a long, unique random ID to each note.
- Puts each one in a different sealed envelope, with a piece of carbon paper.
- Gives envelopes to bank.
- Bank opens 99 envelopes and checks they contain money order for $1000.
- Bank signs the remaining envelope without opening it.
- Bank returns envelope to Alice and deducts $1000 from her account.
- Alice opens envelope, and spends the money order.
- Merchant checks the Bank's signature.
- Merchant deposits money order.
- Bank verifies its signature, checks that the unique random ID has not already been spent, credits Merchant's account, and records the unique random ID.
Blind Signatures
- Alice picks random k between 1 and n.
- Send's Bank t = mke mod n. (e from the Bank's public key.)
- Bank signs t using private key d. Sends Alice:
td = (mke mod n)d mod n = (mke)d mod n  mdked mod n
= (mke)d mod n
mdked mod n
= (mke)d mod n  mdked mod n
mdked mod n mdk mod n.
mdk mod n.
- Alice divides by k to get sm = md mod n.
Digital Cash Protocol (Final)
-
Alice prepares n money orders each containing:
- Amount
- Uniqueness String: X
- Identity Strings: I1 = (h(I1L), h(I1R)), ..., In = (h(InL), h(InR)).
Each (IiL, IiR) pair reveals Alice's identity, I = IiL XOR IiR.
h is a secure, one-way hash function.
- Alice blinds (multiplies by random k) all n money orders and sends them to bank.
- Bank asks for any n - 1 of the random kis and all its corresponding identity strings.
- Bank checks money orders. If okay, signs the remaining blinded money order, and deducts amount from Alice's account.
- Alice unblinds the signed note, and spends it with a Merchant.
- Merchant asks Alice to randomly reveal either IiL or IiR for each i. (Merchant chooses random n-bit selector string.)
- Alice sends Merchant corresponding IiLs or IiRs.
- Merchant uses h to confirm Alice didn't cheat.
- Merchant takes money order and identity string halves to bank.
- Bank verifies its signature, and checks uniqueness string. If it has not been previously deposited, bank credits Merchant and records uniqueness string and identity string halves.
- If it has been previously deposited, bank looks up previous identity string halves. Finds one where both L and R halves are known, and calculates I to identify Alice. Arrests Alice.
- If there are no i's, where different halves are known, arrest Merchant.