Attack of the Clones
06.10.02
A potent and malicious new virus is making its way around the Internet. Brace yourself for a long, hot summer of annoyance and computer meltdowns.
 |
|
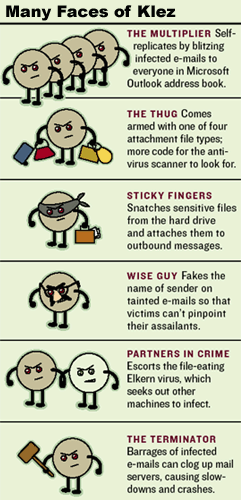
Blame Dyer's overnight celebrity on an eight-month-old virus named Klez, a nasty bit of self-replicating software currently making the rounds on the Internet. (The word "klez" is written in the code, hence the name.) Its modus operandi is to blast e-mails to all the names in Microsoft Outlook's address book, infecting random files on the hard drive and attaching them to outbound messages. The Dyer fan site had to send e-mails to all its new subscribers to confirm their interest.
No one knows yet who wrote Klez. Its first outbreak was in Asia last October. But it is the latest--and potentially scariest--of about 200 worms and viruses circulating on the Net. Klez's newest strains, discovered in mid-April, quickly topped the watch lists of anti-virus software firms like Symantec and Sophos, which say Klez caused 85% of all infections in April.
It's still too early to estimate the cost of Klez, but it is proliferating quickly, thanks in part to its nearly 30 possible subject lines. Some ("A IE 6.0 Patch" and "Your Password") are hard to resist. Others ("How Are You" and "Congratulations") are ridiculously mundane. The last four big epidemics--Nimda, Code Red, Sircam and the I Love You bug--racked up a combined $13 billion in lost productivity and labor costs for cleanup, according to research firm Computer Economics.
While just about anyone can write a virus, teens and college kids on break from school are the most frequent perps. "Kids have more free time on their hands," says April Goostree, virus research manager for McAfee.com.
Sharpei, a new virus Web cops have been tracking, was written by a 16-year-old European cyberchick nicknamed Gigabyte and is thought to be the first to exploit a hole in C#, Microsoft's new programming language. Viruses, worms and other so-called malware exploit programming blunders in software.
At their most benign, viruses eat up precious storage space, slowing or crashing computers. More severe ones destroy or randomly distribute potentially sensitive files. At their worst, viruses are a useful tool to commandeer computers as part of a distributed denial-of-service attack, which paralyzes a site with a barrage of useless data packets. Yahoo and Ebay were downed by such attacks two years ago.
The first Klez strain manipulated a hole in Internet Explorer and tricked the browser into launching infected Outlook e-mail attachments by fiddling with the message's header or instructions for encoding and decoding messages. Klez is so nefarious that you don't have to click on anything to launch it. Simply viewing an Outlook message in the preview window will set it off.
No need to worry about getting blamed, though, since Klez steals names from the address book and sends e-mails under those names and even the anti-virus vendors' names, a trick called spoofing. Microsoft promptly issued a patch, and the virus-scanning firms followed suit with their own updates.
But some Klez strains are so shrewd they can disable virus-scanning features. Open an infected attachment, and you're screwed. Klez also plants another file-damaging virus that targets file-sharing networks. Because of its multiple methods of infection, Klez is considered a "blended threat," one of the most lethal types of viruses. Klez is the first virus since the Nimda worm to reach level four out of a possible five on Symantec's severity scale.
Broadband has increased the speed of infection. Hackers target broadband connections because their IP addresses don't change, making them easier to pin down. High-speed links can send and receive large data files, ideal for sophisticated virus programs. And because broadband is "always on," it often automatically previews e-mails, launching the virus. In the first weekend of May, Symantec received 10,000 Klez alerts from its customers, twice as many as on a typical weekend.
Viruses have come a long way in the last few years. In 1999 the Melissa virus was the first to replicate itself globally via e-mail. (Its 33-year-old creator, David Smith, scored a 20-month prison sentence in early May.) A year later the I Love You virus became the most expensive one to date--$8.7 billion in estimated damage--partly because it quickly organized massive denial-of-service attacks.
Last year's Nimda, a blended threat like Klez, boasted four different ways to invade computers. The greatest fear among virus-busters is what's called a metamorphic virus. These could have the ability to change their code after each time they infect yet another computer, mutating around obstacles much like HIV. Such shape-shifters would evade many virus scanners, which look only for signature chunks of code within an already discovered virus.
Like Klez, future viruses will exploit known security flaws. And there are plenty of those. Last year CERT Coordination Center, the security watch group in Pittsburgh, reported 2,437 security vulnerabilities in software products, up from 171 in 1995. "There's too much pressure on software vendors to get to market quicker," says David Evans, a computer science professor at the University of Virginia. "And there's not enough pressure from the government or legal system for them to get it right."
Some 95% of corporate networks have anti-virus tools in place, but consumers are easy prey. The majority of the 69 million Americans surfing the Net from home do not regularly update their anti-virus scanners (if they even own one) with the latest security patches, despite getting alerts from their anti-virus vendors. Security is only as good as its last update. Research firm Gartner predicts that through 2005, 90% of cyberattacks will exploit security holes for which patches have already been issued.
"If you are in a big company, you have a full-time professional who is actively pushing the patches on users. At home there's nobody pushing you. You don't even know you need it," says William Orvis, a security specialist with the Computer Incident Advisory Capability team, a unit of the Department of Energy.
It is frighteningly easy for aspiring hackers ("script kiddies") to compose viruses from available code, thanks to the estimated 30,000 Web sites offering how-to guides. "You can practically go to Barnes & Noble and buy a book on virus writing," says David Perry, director of education at Trend Micro, an anti-virus software vendor. Used copies of the virus bible, The Giant Black Book of Computer Viruses, are still available online. "Fun for hackers," says one review.
Companies are reluctant to admit they've been victims of cyberattacks, forcing cybercops to play catch-up. One deterrent to companies giving access to investigators is that they don't want them sniffing around corporate documents and hard drives. "The scope of the problem is huge, and law enforcement can only do as much as it gets access to," says Gregory Schaffer, a former Justice Department prosecutor of cybercrime, now head of the computer crime division of PricewaterhouseCoopers.
It gets worse. Viruses have a whole new breeding ground in cell phones and handheld computers. Two years ago Spain's wireless carrier Telefónica suffered the first cellular virus when a worm hit random phones with mean-spirited short messages. Later that year a Trojan horse, a seemingly innocuous program with a built-in backdoor for attackers, caused several of NTT Docomo's cell phones to flood Japan's emergency phone line with calls.
Four known Palm-plaguing threats roam the wild today, spreading by way of synch and beaming features. Some just hide or delete applications, while a Trojan horse called Palm.MTXII will replace notes with gobbledygook. Wi-Fi local area networks are also vulnerable.
"In a doomsday scenario, we could see a threat to tens of millions of PCs that carries over to hundreds of millions of wireless devices," says Stephen Trilling, director of research at Symantec. That scenario isn't far off.